SC-100 Question Includes: Single Choice Questions: 108, Multiple Choice Questions: 30, Hotspot: 55, Drag Drop: 6,
You have an Azure subscription. The subscription contains 50 virtual machines that run Windows Server and 50 virtual machines that run Linux. You need to perform vulnerability assessments on the virtual machines. The solution must meet the following requirements:
• Identify missing updates and insecure configurations.
• Use the Qualys engine.
What should you use?
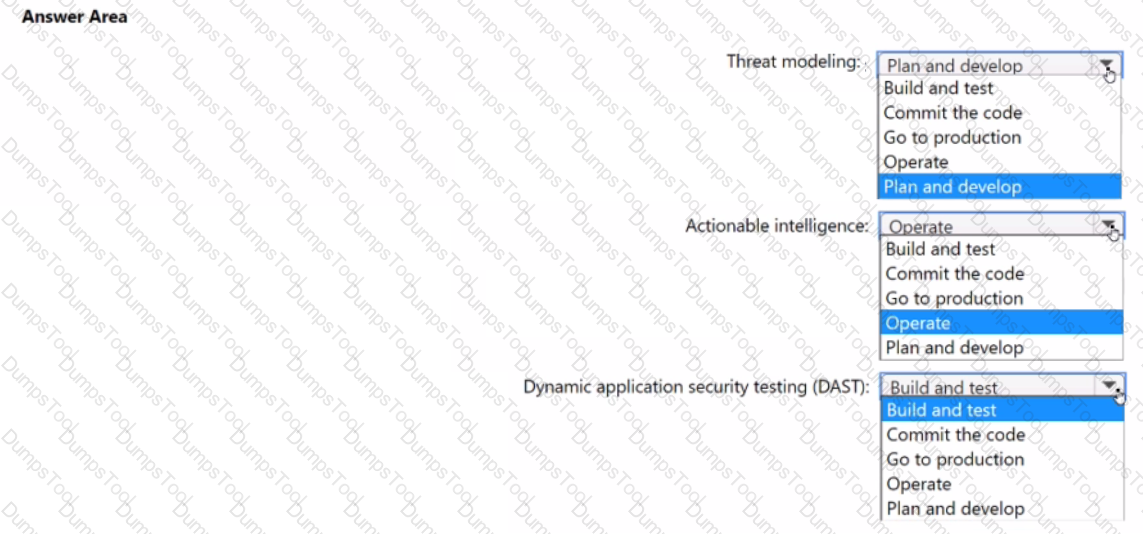
You need to recommend a security methodology for a DevOps development process based on the Microsoft Cloud Adoption Framework for Azure.
During which stage of a continuous integration and continuous deployment (CI/CD) DevOps process should each security-related task be performed? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point
A customer has a hybrid cloud infrastructure that contains a Microsoft 365 E5 subscription and an Azure subscription.
All the on-premises servers in the perimeter network are prevented from connecting directly to the internet.
The customer recently recovered from a ransomware attack.
The customer plans to deploy Microsoft Sentinel.
You need to recommend configurations to meet the following requirements:
• Ensure that the security operations team can access the security logs and the operation logs.
• Ensure that the IT operations team can access only the operations logs, including the event logs of the servers in the perimeter network.
Which two configurations can you include in the recommendation? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
You have an Azure AD tenant that syncs with an Active Directory Domain Services {AD DS) domain. Client computers run Windows and are hybrid-joined to Azure AD.
You are designing a strategy to protect endpoints against ransomware. The strategy follows Microsoft Security Best Practices.
You plan to remove all the domain accounts from the Administrators group on the Windows computers.
You need to recommend a solution that will provide users with administrative access to the Windows computers only when access is required. The solution must minimize the lateral movement of ransomware attacks if an administrator account on a computer is compromised.
What should you include in the recommendation?
Your company has a Microsoft 365 E5 subscription.
The company plans to deploy 45 mobile self-service kiosks that will run Windows 10. You need to provide recommendations to secure the kiosks. The solution must meet the following requirements:
• Ensure that only authorized applications can run on the kiosks.
• Regularly harden the kiosks against new threats.
Which two actions should you include in the recommendations? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
Customers Passed
Microsoft SC-100
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted Microsoft Exam SC-100 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
Microsoft Microsoft Certified: Cybersecurity Architect Expert SC-100 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing Microsoft Microsoft Certified: Cybersecurity Architect Expert SC-100 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool SC-100 Microsoft Cybersecurity Architect Practice Questions is enormous and unmatched!
The SC-100 exam validates your expertise as a Microsoft Cybersecurity Architect. It assesses your ability to design and implement security solutions across hybrid and multicloud environments, leveraging Microsoft security technologies.
The Microsoft SC-100 exam is ideal for professionals who design, implement, and maintain security solutions, including those working in identity and access, platform protection, security operations, data and AI security, application security, and hybrid and multicloud infrastructures.
The SC-100 exam covers designing security solutions for identity, devices, data, AI, applications, network, infrastructure, DevOps, Governance and Risk Compliance (GRC), security operations, and security posture management.
The Microsoft SC-100 exam consists of 40-60 questions.
You need a score of 700 or higher to pass the Microsoft SC-100 exam.
Dumpstool offers comprehensive study materials, including SC-100 real questions, a testing engine, and a study guide, to help candidates grasp key concepts and prepare Microsoft Certified: Cybersecurity Architect Expert confidently. The explanations provided in each question set support both theoretical knowledge and practical application, making it easier for students and professionals to understand and retain information.
Yes, Dumpstool offers SC-100 PDF questions, which you can download and study at your convenience. The PDF format is particularly useful for offline review, and each question includes detailed explanations to reinforce your understanding.
Dumpstool updates its SC-100 exam questions, dumps, and study guides regularly to reflect the latest Microsoft updates and industry changes. This ensures that the SC-100 study materials you receive are current, accurate, and aligned with the exam requirements.
Yes, Dumpstool offers a success guarantee with a money-back policy. If you do not pass the Microsoft Cybersecurity Architect exam after thoroughly using the provided SC-100 practice exam questions answers, Dumpstool allows eligible customers to apply for a refund as per its terms and conditions.