What is the main difference between hypothesis-driven and data-driven Threat Hunting?
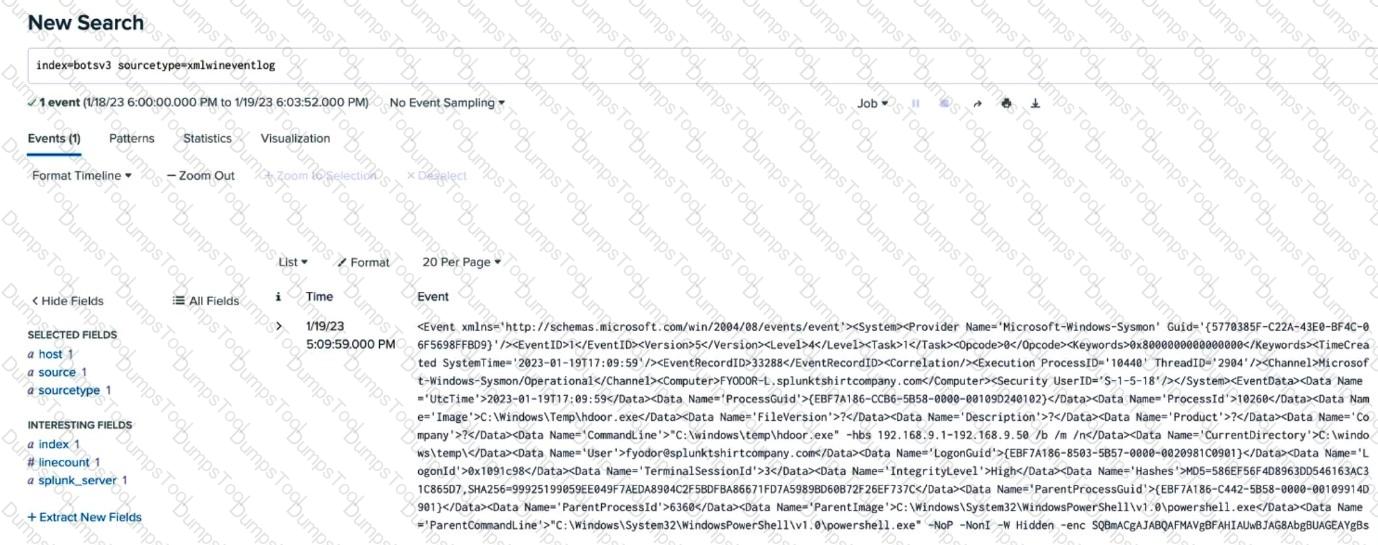
An analyst is building a search to examine Windows XML Event Logs, but the initial search is not returning any extracted fields. Based on the above image, what is themost likelycause?
An analyst needs to create a new field at search time. Which Splunk command will dynamically extract additional fields as part of a Search pipeline?
Which of the following use cases is best suited to be a Splunk SOAR Playbook?
Which stage of continuous monitoring involves adding data, creating detections, and building drilldowns?
A Cyber Threat Intelligence (CTI) team produces a report detailing a specific threat actor’s typical behaviors and intent. This would be an example of what type of intelligence?
A threat hunter generates a report containing the list of users who have logged in to a particular database during the last 6 months, along with the number of times they have each authenticated. They sort this list and remove any user names who have logged in more than 6 times. The remaining names represent the users who rarely log in, as their activity is more suspicious. The hunter examines each of these rare logins in detail.
This is an example of what type of threat-hunting technique?
An analysis of an organization’s security posture determined that a particular asset is at risk and a new process or solution should be implemented to protect it. Typically, who would be in charge of designing the new process and selecting the required tools to implement it?
What device typically sits at a network perimeter to detect command and control and other potentially suspicious traffic?
Which of the following is a correct Splunk search that will return results in the most performant way?
Which of the following Splunk Enterprise Security features allows industry frameworks such as CIS Critical Security Controls, MITRE ATT&CK, and the Lockheed Martin Cyber Kill Chain® to be mapped to Correlation Search results?
The United States Department of Defense (DoD) requires all government contractors to provide adequate security safeguards referenced in National Institute of Standards and Technology (NIST) 800-171. All DoD contractors must continually reassess, monitor, and track compliance to be able to do business with the US government.
Which feature of Splunk Enterprise Security provides an analyst context for the correlation search mapping to the specific NIST guidelines?
When threat hunting for outliers in Splunk, which of the following SPL pipelines would filter for users with over a thousand occurrences?