Which activity below is NOT included in the information security risk assessment process?
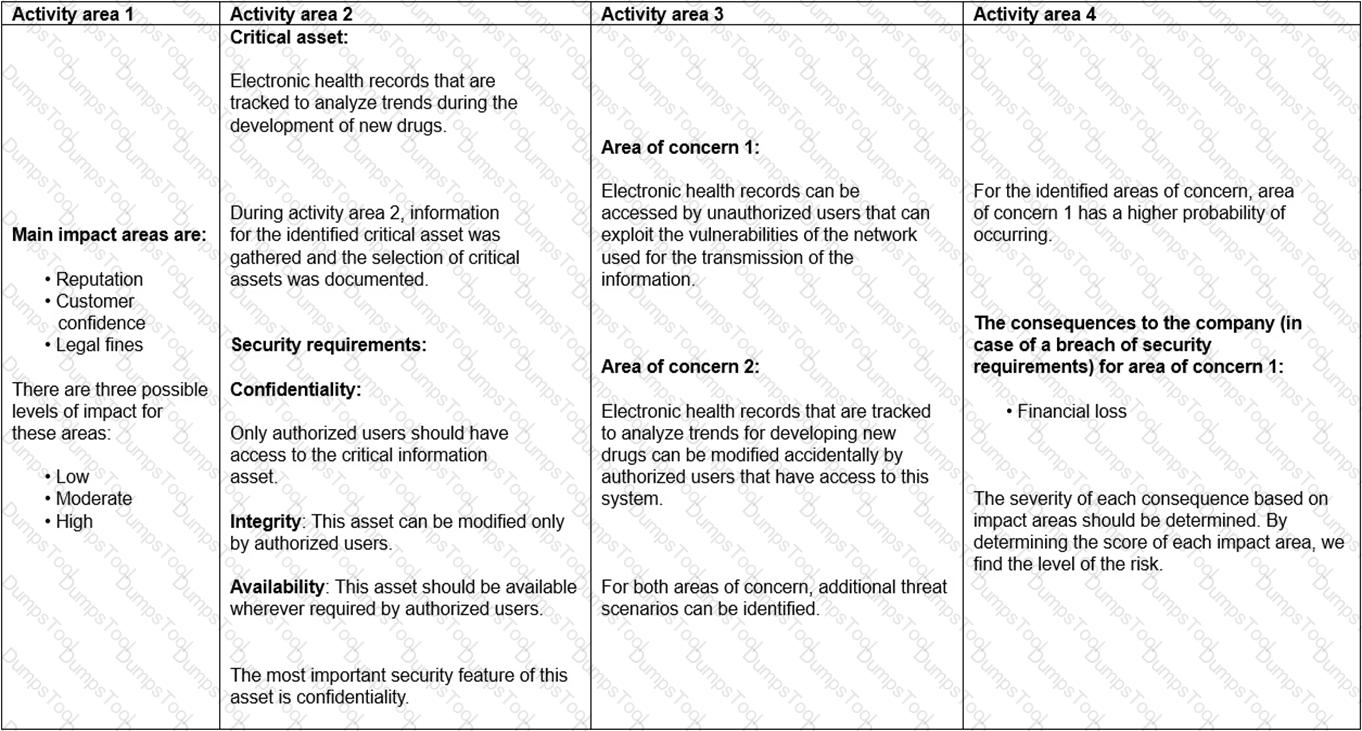
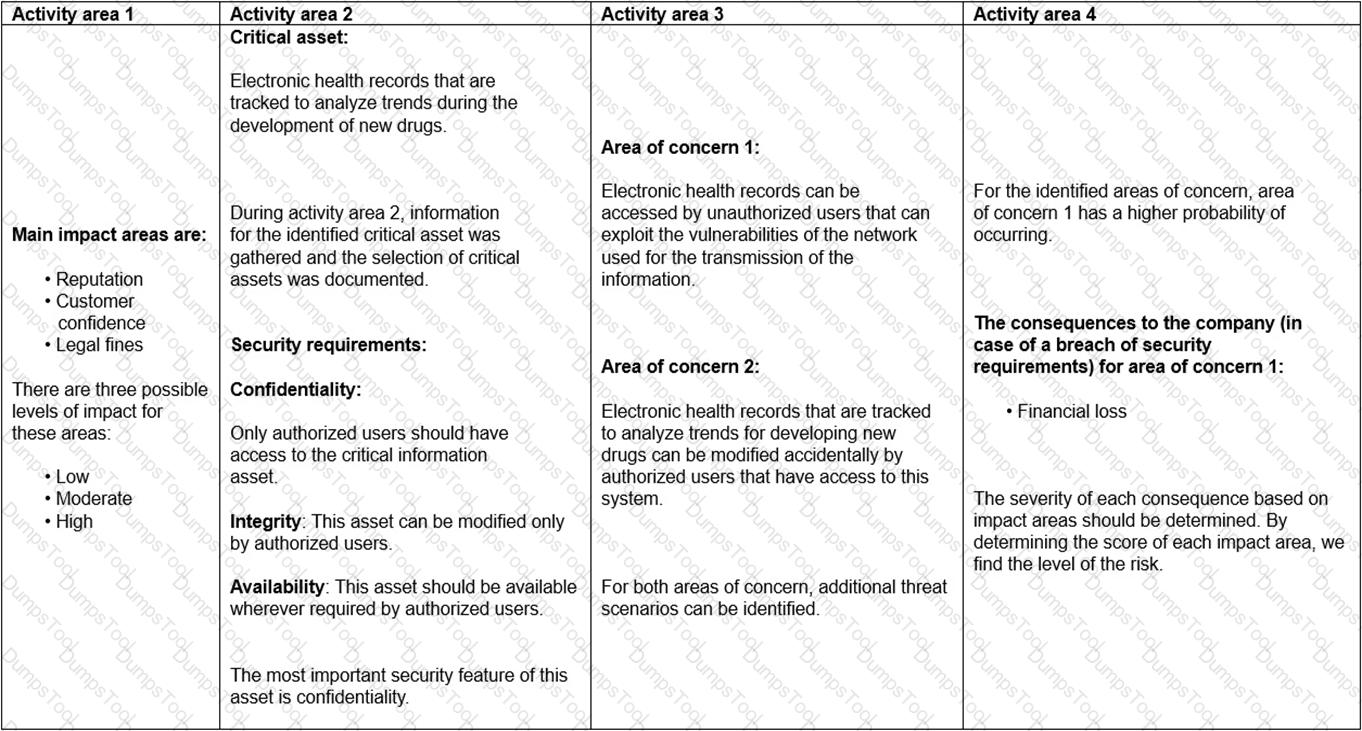
Scenario 8: Biotide is a pharmaceutical company that produces medication for treating different kinds of diseases. The company was founded in 1997, and since then it has contributed in solving some of the most challenging healthcare issues.
As a pharmaceutical company, Biotide operates in an environment associated with complex risks. As such, the company focuses on risk management strategies that ensure the effective management of risks to develop high-quality medication. With the large amount of sensitive information generated from the company, managing information security risks is certainly an important part of the overall risk management process. Biotide utilizes a publicly available methodology for conducting risk assessment related to information assets. This methodology helps Biotide to perform risk assessment by taking into account its objectives and mission. Following this method, the risk management process is organized into four activity areas, each of them involving a set of activities, as provided below.
1. Activity area 1: The organization determines the criteria against which the effects of a risk occurring can be evaluated. In addition, the impacts of risks are also defined.
2. Activity area 2: The purpose of the second activity area is to create information asset profiles. The organization identifies critical information assets, their owners, as well as the security requirements for those assets. After determining the security requirements, the organization prioritizes them. In addition, the organization identifies the systems that store, transmit, or process information.
3. Activity area 3: The organization identifies the areas of concern which initiates the risk identification process. In addition, the organization analyzes and determines the probability of the occurrence of possible threat scenarios.
4. Activity area 4: The organization identifies and evaluates the risks. In addition, the criteria specified in activity area 1 is reviewed and the consequences of the areas of concerns are evaluated. Lastly, the level of identified risks is determined.
The table below provides an example of how Biotide assesses the risks related to its information assets following this methodology:
According to the risk assessment methodology used by Biotide, what else should be performed during activity area 4? Refer to scenario 8.
Scenario 5: Detika is a private cardiology clinic in Pennsylvania, the US. Detika has one of the most advanced healthcare systems for treating heart diseases. The clinic uses sophisticated apparatus that detects heart diseases in early stages. Since 2010, medical information of Detika’s patients is stored on the organization’s digital systems. Electronic health records (EHR), among others, include patients’ diagnosis, treatment plan, and laboratory results.
Storing and accessing patient and other medical data digitally was a huge and a risky step for Detika. Considering the sensitivity of information stored in their systems, Detika conducts regular riskassessments to ensure that all information security risks are identified and managed. Last month, Detika conducted a risk assessment which was focused on the EHR system. During risk identification, the IT team found out that some employees were not updating the operating systems regularly. This could cause major problems such as a data breach or loss of software compatibility. In addition, the IT team tested the software and detected a flaw in one of the software modules used. Both issues were reported to the top management and they decided to implement appropriate controls for treating the identified risks. They decided to organize training sessions for all employees in order to make them aware of the importance of the system updates. In addition, the manager of the IT Department was appointed as the person responsible for ensuring that the software is regularly tested.
Another risk identified during the risk assessment was the risk of a potential ransomware attack. This risk was defined as low because all their data was backed up daily. The IT team decided to accept the actual risk of ransomware attacks and concluded that additional measures were not required. This decision was documented in the risk treatment plan and communicated to the risk owner. The risk owner approved the risk treatment plan and documented the risk assessment results.
Following that, Detika initiated the implementation of new controls. In addition, one of the employees of the IT Department was assigned the responsibility for monitoring the implementation process and ensure the effectiveness of the security controls. The IT team, on the other hand, was responsible for allocating the resources needed to effectively implement the new controls.
Based on scenario 5, the decision to accept the risk of a potential ransomware attack was approved by the risk owner. Is this acceptable?
Scenario 2: Travivve is a travel agency that operates in more than 100 countries. Headquartered in San Francisco, the US, the agency is known for its personalized vacation packages and travel services. Travivve aims to deliver reliable services that meet its clients’ needs. Considering the impact of information security in its reputation, Travivve decided to implement an information security management system (ISMS) based on ISO/IEC 27001. In addition, they decided to establish and implement an information security risk management program. Based on the priority of specific departments in Travivve, the top management decided to initially apply the risk management process only in the Sales Management Department. The process would be applicable for other departments only when introducing new technology.
Travivve’s top management wanted to make sure that the risk management program is established based on the industry best practices. Therefore, they created a team of three members that would be responsible for establishing and implementing it. One of the team members was Travivve’s risk manager who was responsible for supervising the team and planning all risk management activities. In addition, the risk manager was responsible for monitoring the program and reporting the monitoring results to the top management.
Initially, the team decided to analyze the internal and external context of Travivve. As part of the process of understanding the organization and its context, the team identified key processes and activities. Then, the team identified the interested parties and their basic requirements and determinedthe status of compliance with these requirements. In addition, the team identified all the reference documents that applied to the defined scope of the risk management process, which mainly included the Annex A of ISO/IEC 27001 and the internal security rules established by Travivve. Lastly, the team analyzed both reference documents and justified a few noncompliances with those requirements.
The risk manager selected the information security risk management method which was aligned with other approaches used by the company to manage other risks. The team also communicated the risk management process to all interested parties through previously established communication mechanisms. In addition, they made sure to inform all interested parties about their roles and responsibilities regarding risk management. Travivve also decided to involve interested parties in its risk management activities since, according to the top management, this process required their active participation.
Lastly, Travivve’s risk management team decided to conduct the initial information security risk assessment process. As such, the team established the criteria for performing the information security risk assessment which included the consequence criteria and likelihood criteria.
Did Travivve’s risk management team identify the basic requirements of interested parties in accordance with the guidelines of ISO/IEC 27005? Refer to scenario 2.
Scenario 7: Adstry is a business growth agency that specializes in digital marketing strategies. Adstry helps organizations redefine the relationships with their customers through innovative solutions. Adstry is headquartered in San Francisco and recently opened two new offices in New York. The structure of the company is organized into teams which are led by project managers. The project manager has the full power in any decision related to projects. The team members, on the other hand, report the project’s progress to project managers.
Considering that data breaches and ad fraud are common threats in the current business environment, managing risks is essential for Adstry. When planning new projects, each project manager is responsible for ensuring that risks related to a particular project have been identified, assessed, and mitigated. This means that project managers have also the role of the risk manager in Adstry. Taking into account that Adstry heavily relies on technology to complete their projects, their risk assessment certainly involves identification of risks associated with the use of information technology. At the earliest stages of each project, the project manager communicates the risk assessment results to its team members.
Adstry uses a risk management software which helps the project team to detect new potential risks during each phase of the project. This way, team members are informed in a timely manner for the new potential risks and are able to respond to them accordingly. The project managers are responsible forensuring that the information provided to the team members is communicated using an appropriate language so it can be understood by all of them.
In addition, the project manager may include external interested parties affected by the project in the risk communication. If the project manager decides to include interested parties, the risk communication is thoroughly prepared. The project manager firstly identifies the interested parties that should be informed and takes into account their concerns and possible conflicts that may arise due to risk communication. The risks are communicated to the identified interested parties while taking into consideration the confidentiality of Adstry’s information and determining the level of detail that should be included in the risk communication. The project managers use the same risk management software for risk communication with external interested parties since it provides a consistent view of risks. For each project, the project manager arranges regular meetings with relevant interested parties of the project, they discuss the detected risks, their prioritization, and determine appropriate treatment solutions. The information taken from the risk management software and the results of these meetings are documented and are used for decision-making processes. In addition, the company uses a computerized documented information management system for the acquisition, classification, storage, and archiving of its documents.
Based on scenario 7, which principle of efficient communication strategy Adstry’s project managers follow when communicating risks to team members?
Scenario 3: Printary is an American company that offers digital printing services. Creating cost-effective and creative products, the company has been part of the printing industry for more than 30 years. Three years ago, the company started to operate online, providing greater flexibility for its clients. Through the website, clients could find information about all services offered by Printary and order personalized products. However, operating online increased the risk of cyber threats, consequently, impacting the business functions of the company. Thus, along with the decision of creating an online business, the company focused on managing information security risks. Their risk management program was established based on ISO/IEC 27005 guidelines and industry best practices.
Last year, the company considered the integration of an online payment system on its website in order to provide more flexibility and transparency to customers. Printary analyzed various available solutions and selected Pay0, a payment processing solution that allows any company to easily collect payments on their website. Before making the decision, Printary conducted a risk assessment to identify and analyze information security risks associated with the software. The risk assessment process involved three phases: identification, analysis, and evaluation. During risk identification, the company inspected assets, threats, and vulnerabilities. In addition, to identify the information security risks, Printary used a list ofthe identified events that could negatively affect the achievement of information security objectives. The risk identification phase highlighted two main threats associated with the online payment system: error in use and data corruption After conducting a gap analysis, the company concluded that the existing security controls were sufficient to mitigate the threat of data corruption. However, the user interface of the payment solution was complicated, which could increase the risk associated with user errors, and, as a result, impact data integrity and confidentiality.
Subsequently, the risk identification results were analyzed. The company conducted risk analysis in order to understand the nature of the identified risks. They decided to use a quantitative risk analysis methodology because it would provide more detailed information. The selected risk analysis methodology was consistent with the risk evaluation criteria. Firstly, they used a list of potential incident scenarios to assess their potential impact. In addition, the likelihood of incident scenarios was defined and assessed. Finally, the level of risk was defined as low.
In the end, the level of risk was compared to the risk evaluation and acceptance criteria and was prioritized accordingly.
Based on scenario 3, what does the complicated user interface of the software which could lead to error present?
According to ISO/IEC 27000, what is the definition of information security?
Scenario 5: Detika is a private cardiology clinic in Pennsylvania, the US. Detika has one of the most advanced healthcare systems for treating heart diseases. The clinic uses sophisticated apparatus that detects heart diseases in early stages. Since 2010, medical information of Detika’s patients is stored on the organization’s digital systems. Electronic health records (EHR), among others, include patients’ diagnosis, treatment plan, and laboratory results.
Storing and accessing patient and other medical data digitally was a huge and a risky step for Detika. Considering the sensitivity of information stored in their systems, Detika conducts regular risk assessments to ensure that all information security risks are identified and managed. Last month, Detika conducted a risk assessment which was focused on the EHR system. During risk identification, the IT team found out that some employees were not updating the operating systems regularly. This could cause major problems such as a data breach or loss of software compatibility. In addition, the IT team tested the software and detected a flaw in one of the software modules used. Both issues were reported to the top management and they decided to implement appropriate controls for treating the identified risks. They decided to organize training sessions for all employees in order to make them aware of the importance of the system updates. In addition, the manager of the IT Department was appointed as the person responsible for ensuring that the software is regularly tested.
Another risk identified during the risk assessment was the risk of a potential ransomware attack. This risk was defined as low because all their data was backed up daily. The IT team decided to accept the actual risk of ransomware attacks and concluded that additional measures were not required. This decision was documented in the risk treatment plan and communicated to the risk owner. The risk owner approved the risk treatment plan and documented the risk assessment results.
Following that, Detika initiated the implementation of new controls. In addition, one of the employees of the IT Department was assigned the responsibility for monitoring the implementation process and ensure the effectiveness of the security controls. The IT team, on the other hand, was responsible for allocating the resources needed to effectively implement the new controls.
Based on scenario 5, the IT team was responsible for allocating the necessary resources to ensure that the new controls are implemented effectively. Is this acceptable?
Scenario 3: Printary is an American company that offers digital printing services. Creating cost-effective and creative products, the company has been part of the printing industry for more than 30 years. Three years ago, the company started to operate online, providing greater flexibility for its clients. Through the website, clients could find information about all services offered by Printary and order personalized products. However, operating online increased the risk of cyber threats, consequently, impacting the business functions of the company. Thus, along with the decision of creating an online business, the company focused on managing information security risks. Their risk management program was established based on ISO/IEC 27005 guidelines and industry best practices.
Last year, the company considered the integration of an online payment system on its website in order to provide more flexibility and transparency to customers. Printary analyzed various available solutions and selected Pay0, a payment processing solution that allows any company to easily collect payments on their website. Before making the decision, Printary conducted a risk assessment to identify and analyze information security risks associated with the software. The risk assessment process involved three phases: identification, analysis, and evaluation. During risk identification, the company inspected assets, threats, and vulnerabilities. In addition, to identify the information security risks, Printary used a list of the identified events that could negatively affect the achievement of information security objectives. The risk identification phase highlighted two main threats associated with the online payment system: error in use and data corruption After conducting a gap analysis, the company concluded that the existing security controls were sufficient to mitigate the threat of data corruption. However, the user interface of the payment solution was complicated, which could increase the risk associated with user errors, and, as a result, impact data integrity and confidentiality.
Subsequently, the risk identification results were analyzed. The company conducted risk analysis in order to understand the nature of the identified risks. They decided to use a quantitative risk analysis methodology because it would provide more detailed information. The selected risk analysis methodology was consistent with the risk evaluation criteria. Firstly, they used a list of potential incident scenarios to assess their potential impact. In addition, the likelihood of incident scenarios was defined and assessed. Finally, the level of risk was defined as low.
In the end, the level of risk was compared to the risk evaluation and acceptance criteria and was prioritized accordingly.
Based on scenario 3, Printary used a list of identified events that could negatively influence the achievement of its information security objectives to identify information security risks. Is this in compliance with the guidelines of ISO/IEC 27005?
Scenario 3: Printary is an American company that offers digital printing services. Creating cost-effective and creative products, the company has been part of the printing industry for more than 30 years. Three years ago, the company started to operate online, providing greater flexibility for its clients. Through the website, clients could find information about all services offered by Printary and order personalized products. However, operating online increased the risk of cyber threats, consequently, impacting the business functions of the company. Thus, along with the decision of creating an online business, the company focused on managing information security risks. Their risk management program was established based on ISO/IEC 27005 guidelines and industry best practices.
Last year, the company considered the integration of an online payment system on its website in order to provide more flexibility and transparency to customers. Printary analyzed various available solutions and selected Pay0, a payment processing solution that allows any company to easily collect payments on their website. Before making the decision, Printary conducted a risk assessment to identify and analyze information security risks associated with the software. The risk assessment process involved three phases: identification, analysis, and evaluation. During risk identification, the company inspected assets, threats, and vulnerabilities. In addition, to identify the information security risks, Printary used a list of the identified events that could negatively affect the achievement of information security objectives. The risk identification phase highlighted two main threats associated with the online payment system: error in use and data corruption After conducting a gap analysis, the company concluded that the existing security controls were sufficient to mitigate the threat of data corruption. However, the user interface of the payment solution was complicated, which could increase the risk associated with user errors, and, as a result, impact data integrity and confidentiality.
Subsequently, the risk identification results were analyzed. The company conducted risk analysis in order to understand the nature of the identified risks. They decided to use a quantitative risk analysis methodology because it would provide more detailed information. The selected risk analysis methodology was consistent with the risk evaluation criteria. Firstly, they used a list of potential incident scenarios to assess their potential impact. In addition, the likelihood of incident scenarios was defined and assessed. Finally, the level of risk was defined as low.
In the end, the level of risk was compared to the risk evaluation and acceptance criteria and was prioritized accordingly.
Did Primary perform risk analysis in accordance with the guidelines of ISO/IEC 27005? Refer to scenario 3.
Scenario 3: Printary is an American company that offers digital printing services. Creating cost-effective and creative products, the company has been part of the printing industry for more than 30 years. Three years ago, the company started to operate online, providing greater flexibility for its clients. Through the website, clients could find information about all services offered by Printary and order personalized products. However, operating online increased the risk of cyber threats, consequently, impacting the business functions of the company. Thus, along with the decision of creating an online business, the company focused on managing information security risks. Their risk management program was established based on ISO/IEC 27005 guidelines and industry best practices.
Last year, the company considered the integration of an online payment system on its website in order to provide more flexibility and transparency to customers. Printary analyzed various available solutions and selected Pay0, a payment processing solution that allows any company to easily collect payments on their website. Before making the decision, Printary conducted a risk assessment to identify and analyze information security risks associated with the software. The risk assessment process involved three phases: identification, analysis, and evaluation. During risk identification, the company inspected assets, threats, and vulnerabilities. In addition, to identify the information security risks, Printary used a list of the identified events that could negatively affect the achievement of information security objectives. The risk identification phase highlighted two main threats associated with the online payment system: error in use and data corruption After conducting a gap analysis, the company concluded that the existing security controls were sufficient to mitigate the threat of data corruption. However, the user interface of the payment solution was complicated, which could increase the risk associated with user errors, and, as a result, impact data integrity and confidentiality.
Subsequently, the risk identification results were analyzed. The company conducted risk analysis in order to understand the nature of the identified risks. They decided to use a quantitative risk analysis methodology because it would provide more detailed information. The selected risk analysis methodology was consistent with the risk evaluation criteria. Firstly, they used a list of potential incident scenarios to assess their potential impact. In addition, the likelihood of incident scenarios was defined and assessed. Finally, the level of risk was defined as low.
In the end, the level of risk was compared to the risk evaluation and acceptance criteria and was prioritized accordingly.
Based on the scenario above, answer the following question:
What type of risk identification approach did Printary use?
Scenario 8: Biotide is a pharmaceutical company that produces medication for treating different kinds of diseases. The company was founded in 1997, and since then it has contributed in solving some of the most challenging healthcare issues.
As a pharmaceutical company, Biotide operates in an environment associated with complex risks. As such, the company focuses on risk management strategies that ensure the effective management of risks to develop high-quality medication. With the large amount of sensitive information generated from the company, managing information security risks is certainly an important part of the overall risk management process. Biotide utilizes a publicly available methodology for conducting risk assessment related to information assets. This methodology helps Biotide to perform risk assessment by taking into account its objectives and mission. Following this method, the risk management process is organized into four activity areas, each of them involving a set of activities, as provided below.
1. Activity area 1: The organization determines the criteria against which the effects of a risk occurring can be evaluated. In addition, the impacts of risks are also defined.
2. Activity area 2: The purpose of the second activity area is to create information asset profiles. The organization identifies critical information assets, their owners, as well as the security requirements for those assets. After determining the security requirements, the organization prioritizes them. In addition, the organization identifies the systems that store, transmit, or process information.
3. Activity area 3: The organization identifies the areas of concern which initiates the risk identification process. In addition, the organization analyzes and determines the probability of the occurrence of possible threat scenarios.
4. Activity area 4: The organization identifies and evaluates the risks. In addition, the criteria specified in activity area 1 is reviewed and the consequences of the areas of concerns are evaluated. Lastly, the level of identified risks is determined.
The table below provides an example of how Biotide assesses the risks related to its information assets following this methodology:
Based on the table provided in scenario 8, did Biotide follow all the steps of the risk assessment methodology regarding the identification of assets?