Which method should an administrator use to make sure all data In a local tier cannot be read If the underlying device Is repurposed, returned, misplaced, or stolen?
Which three are required licenses for Fabric Attached MetroCluster? (Choose 3)
An administrator Is troubleshooting failed cluster peering between three ONTAP clusters for cascaded SnapMirror replication. Cluster1 is peered to Cluster, cluster^ is peered to Cluster3.
Clusterl and Cluster3 do not have an available route to reach each other. Cluster2 can route to both Cluster1 and Cluster3 using dedicated and separate intercluster LIFs.
What ONTAP network component must be configured on Cluster2 to resolve this issue?
A NearStore system or storage appliance can operate as a secondary and primary system at the same time.
One method of configuring an interface for takeover is to enter ifconfig interface partner address at the command line. To make tins configuration persistent across reboots, you must enter tins information in the_____file for each appliance.
Which two commands could be used if the cf giveback command foils? (Choose 2)
Which command allows yon to access the other nodes console after a takeover has occurred?
A volume is SnapMirrored hourly. You revert the volume using a snapshot that was created two days ago. Which command continues the relationship?
You are troubleshooting a clustered failover problem at a customer site. The customer explains that both storage appliances were NFS mounted onto the Solaris host. You attempt to create a file on the NFS mount point for the inaccessible appliance, but you get the following error:NFS server filer2 not responding still trying.Symptoms:
1) When not in takeover mode, both storage appliances operate normally.
2) In takeover mode, the taken over node is not accessible on the network.You perform a "cf giveback" and you can now create a file over NFS on both appliances.
What should vou do first to resolve this issue?
Which two networking components must be configured to failover LIFs across subnets? (Choose two.)
What command would you enter to restore the /vol/flexvol0/etc/rc file from a snapshot to the /vol/flexvol0/home directory?
Which one of the following commands or procedures would you use to undo a SnapRestore reversion?
The OSSV agent on the primary system listens to TCP port 10000 for all SnapVault communications.
Refer to the exhibit.
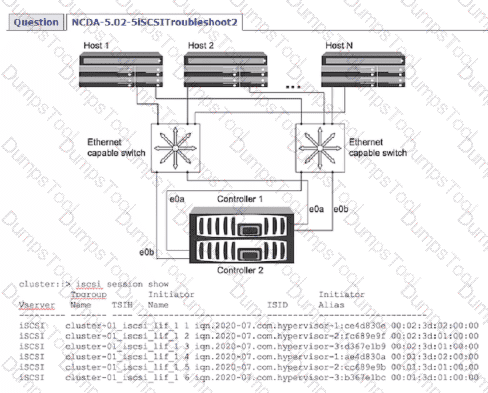
A company has three servers that are using the iSCSI protocol to connect to a two node NetApp ONTAP cluster. The server administrator notices that half of the paths are down. The administrator checks the ONTAP cluster and notices the servers are logging into only the first controller.
Which two steps should the administrator take to troubleshoot the issue? (Choose two.)
Which ONTAP feature discards identical blocks and replaces them with references to a single shared block?
An aggregate is composed of twelve 36-Gigabyte disks. A drive fails and only 72-Gigabyte spare disks are available Data ONTAP will then perform what action?
Identify the two SnapMirror commands that are entered on the source storage appliance.
If an error message indicates that the cluster interconnect adapter itself is faulty, what is your corrective action?
What needs to be enabled on an ONTAP SMB share to increase data throughput and fault tolerance for Microsoft SQL Server databases?
Which two Interfaces can an administrator use to disable unused Ethernet ports on an ONTAP cluster? (Choose two.)
What is the maximum number of disk shelves per loop in a fabric-attached MetroCluster?
Fill in the blank for the following statement using the best answer from the choices that follow. A snapshot is a frozen, read-only image of the entire Data ONTAP file system that reflects the state of the____________at the time the snapshot was created.
Which two protocols provide NAS access for home directories on an S VM? (Choose two.)
Which two options must be configured to use tamperproof snapshots? (Choose two.)
You have determined that the failure to a MetroChister is a disaster. Which step should you take?
Which command disables client access to Snapshot copies on a volume called flexvol1?
Which two configurations ensure end users are able to restore previous versions of files? (Choose two.)
Which MetroCluster configuration procedure is recommended for re-establishing a mirrored volume that was in a level-0 re synchronization state when it failed?
Which one of the following commands is used to specify the destination appliance(s) that are allowed to replicate (pul data from the source appliance?
In a Fabric Attached Metro Cluster, disk ownership by a node is determined by_____________.
Which three tools present statistics from the Data ONTAP counter manager? (Choose three.)
How can you "throttle" Snap Vault updates and baseline transfers so that the primary or secondary is not transmitting data as fast as it can?
After an unexpected ONTAP node reboot, an administrator notices that the NAS data LIFs are not on their home port.
Which UF configuration would modify this behavior?
Which SyncMirror command mirrors an existing unmirrored aggregate where Data ONTAP selects the disk drives?
Due to the sensitive nature of AutoSupport messages, what transport protocol should a storage administrator configure?
Which two default HA features work together to reduce and avoid client outages on an ONTAP FAS cluster? (Choose two.)
Which one of the following statements apply to the Free Space Estimator utility?
What two actions occur automatically if the system detects ransomware activity when Autonomous Ransomware Protection is enabled? (Choose two.)
Which one of the following is not recommended asasecondary system forSnapVault?
Which option of the snap restore command allows you to specify a different directory, as long as the directory already exists?
Which one of the following /etc/snapmirror.conf entries will not support synchronous SnapMirror?