Which of the following statements is false about Eth-Trunk?(Select All that Apply)
When Eth-Trunk is deployed for the heartbeat links between firewalls, the Eth-Trunk interface can be configured as a Layer 2 interface as long as the total bandwidth of active links on the Eth-Trunk is greater than 30% of the bandwidth required by service traffic.
In a Huawei network security environment, which of the following is a key advantage of using HWTACACS over RADIUS for device management authentication?
Options:
Predefined URL categories on Huawei firewalls reside in the URL category database delivered with the device and do not need to be manually loaded.
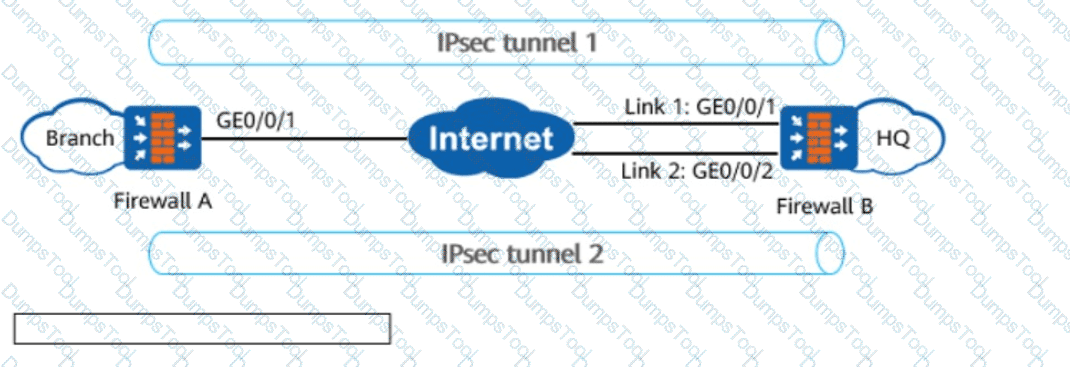
In the figure, enterprise A and enterprise B need to communicate securely, and an IPsec tunnel is established between firewall A and firewall B. Which of the following security protocols and encapsulation modes can meet the requirements of this scenario?
Which of the following conditions can be matched by PBR?(Select All that Apply)
In the figure, FW_A connects to FW_B through two links working in active/standby mode. When the active link of FW_A is faulty, the old IPsec tunnel 1 needs to be torn down, and IPsec tunnel 2 needs to be established with FW_B through the standby link to route traffic. In this case, configuring the IKE _____ detection mechanism on FW_A helps detect link faults and tear down the IPsec tunnel.(Enter lowercase letters.)
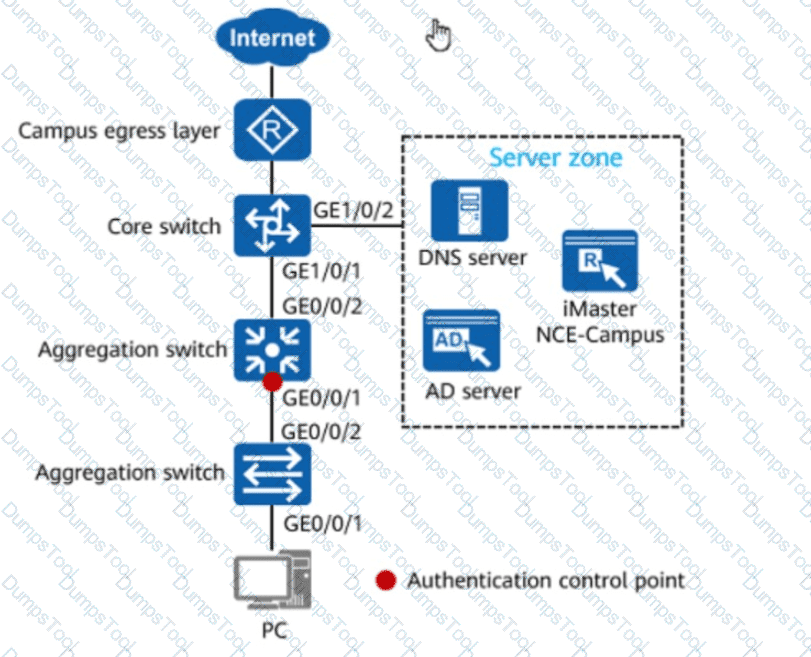
In the figure, if 802.1X authentication is used for wired users on the network, the network admission device and terminals must be connected through a Layer 2 network.
Options:
Which of the following is the function of Message 1 and Message 2 during IKEv1 phase-1 negotiation in main mode?
In quota control policies, which of the following can be set for users?(Select All that Apply)
Multiple links can be deployed at the egress of an enterprise network to improve network reliability.
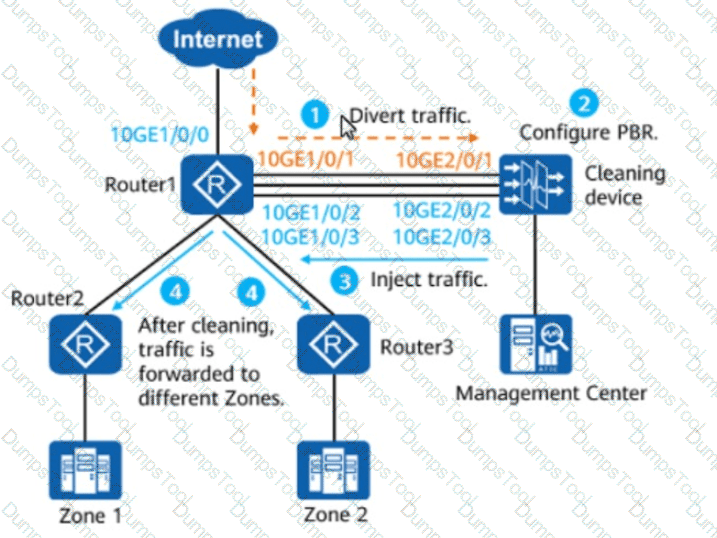
The figure shows the PBR-based injection scenario. Which of the following statements are true about this scenario?(Select All that Apply)