In a default CyberArk installation, which group must a user be a member of to view the “reports” page in PVWA?
According to the DEFAULT Web Options settings, which group grants access to the REPORTS page?
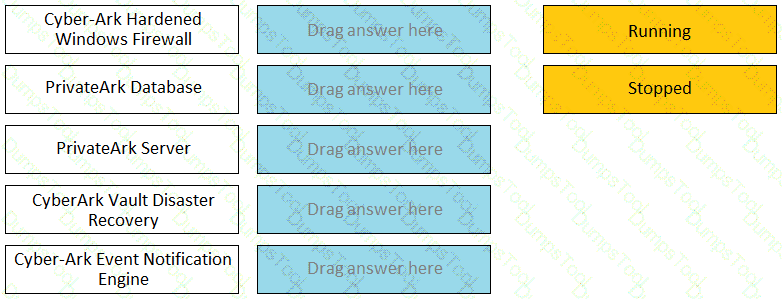
Match the Status of Service on a DR Vault to what is displayed when it is operating normally in Replication mode.
You need to move a platform from using PMTerminal to using Terminal Plugin Controller (TPC) What must you do?
You need to recover an account localadmin02 for target server 10.0.123.73 stored in Safe Team1.
What do you need to recover and decrypt the object? (Choose three.)
For a safe with Object Level Access enabled you can turn off Object Level Access Control when it no longer needed on the safe.
When a DR Vault Server becomes an active vault, it will automatically fail back to the original state once the Primary Vault comes back online.
Which step is required to register a Vault manually in Amazon Web Services using CAVaultManager?
You are logging into CyberArk as the Master user to recover an orphaned safe.
Which items are required to log in as Master?
CyberArk user Neil is trying to connect to the Target Linux server 192.168.1.64 using a domain account ACME/linuxuser01 on Domain Acme.corp using PSM for SSH server 192.168.65.145. What is the correct syntax?
What is the configuration file used by the CPM scanner when scanning UNIX/Linux devices?
What is a prerequisite step before CyberArk can be configured to support RADIUS authentication?
You have been asked to design the number of PVWAs a customer must deploy. The customer has three data centers with a distributed vault in each, requires high availability, and wants to use all vaults, at all times. How many PVWAs does the customer need?
It is possible to restrict the time of day, or day of week that a [b]verify[/b] process can occur
Which of the following PTA detections require the deployment of a Network Sensor or installing the PTA Agent on the domain controller?
One can create exceptions to the Master Policy based on ____________________.
Can the 'Connect' button be used to initiate an SSH connection, as root, to a Unix system when SSH access for root is denied?
You are installing multiple PVWAs behind a load balancer. Which statement is correct?
Which onboarding method would you use to integrate CyberArk with your accounts provisioning process?
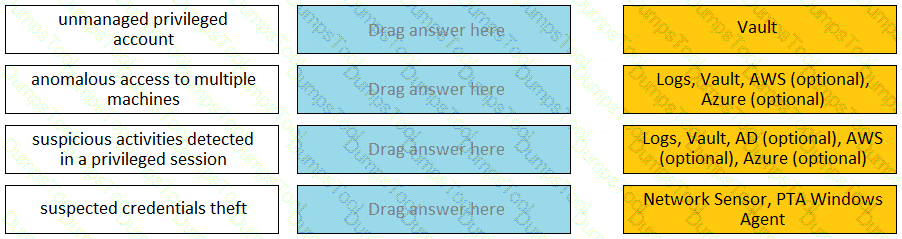
Match each PTA alert category with the PTA sensors that collect the data for it.
A customer is deploying PVWAs in the Amazon Web Services Public Cloud. Which load balancing option does CyberArk recommend?
Time of day or day of week restrictions on when password verifications can occur configured in ____________________.
You are helping a customer prepare a Windows server for PSM installation. What is required for a successful installation?
In order to connect to a target device through PSM, the account credentials used for the connection must be stored in the vault?
Users can be resulted to using certain CyberArk interfaces (e.g.PVWA or PACLI).
Due to network activity, ACME Corp’s PrivateArk Server became active on the OR Vault while the Primary Vault was also running normally. All the components continued to point to the Primary Vault.
Which steps should you perform to restore DR replication to normal?
You are creating a Dual Control workflow for a team’s safe.
Which safe permissions must you grant to the Approvers group?
A new domain controller has been added to your domain. You need to ensure the CyberArk infrastructure can use the new domain controller for authentication.
Which locations must you update?
Which type of automatic remediation can be performed by the PTA in case of a suspected credential theft security event?
A customer is moving from an on-premises to a public cloud deployment. What is the best and most cost-effective option to secure the server key?
Which Cyber Are components or products can be used to discover Windows Services or Scheduled Tasks that use privileged accounts? Select all that apply.
In addition to disabling Windows services or features not needed for PVWA operations, which tasks does PVWA Hardening.ps1 perform when run?
You have associated a logon account to one your UNIX cool accounts in the vault. When attempting to [b]change [/b] the root account’s password the CPM will…..
When a DR Vault Server becomes an active vault, it will automatically revert back to DR mode once the Primary Vault comes back online.
As long as you are a member of the Vault Admins group, you can grant any permission on any safe that you have access to.
For Digital Vault Cluster in a high availability configuration, how does the cluster determine if a node is down?
It is possible to control the hours of the day during which a user may log into the vault.
Which of the following Privileged Session Management solutions provide a detailed audit log of session activities?
You have been asked to limit a platform called "Wmdows_Servers" to safes called "WindowsDCT and "WindowsDC2" The platform must not be assigned to any other safe What is the correct way to accomplish this?
Which permissions are needed for the Active Directory user required by the Windows Discovery process?